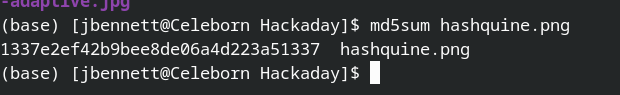
A hashquine is a entertaining way to show off your crypto-tips — It’s a file that is made up of its possess hash. In some file types it is trivial, you just pick the hash to hit, and then place random knowledge in a comment or other invisible subject till you get a collision. A Python script that prints its very own hash would be uncomplicated. But not each file style is so quick. Get PNG for occasion. these data files are split into chunks of information, and each individual chunk is each CRC-32 and adler32 checksummed. Make one particular alter, and every little thing changes, in a few places at the moment. Fantastic luck obtaining that collision. So how exactly did [David Buchanan] crank out that lovely PNG, which does in truth md5sum to the price in the impression? Quite cleverly.
Many thanks to [Julian] for the idea! And as he explained it, this hack is a person that receives extra outstanding the additional you imagine about it. Appreciate!






More Stories
7 downsides of open source culture
iPhone 15 And 15 Plus Price Tag Could Be Lowered To Increase Adoptability
Turn A Webpage Into A Desktop App With Gluon